Author: cslab
-

🔑 Does Key Rotation Re-encrypt All Data? — The Truth About Cloud KMS
“Rotate your keys periodically” sounds simple enough… but does it mean re-encrypting terabytes of data? 😱 ## ## 🎯 What this article covers What “key rotation” actually means in Cloud KMS The concept of Envelope Encryption — without it, you’ll never understand key rotation Comparison of key rotation behavior in AWS KMS vs Azure Key…
-
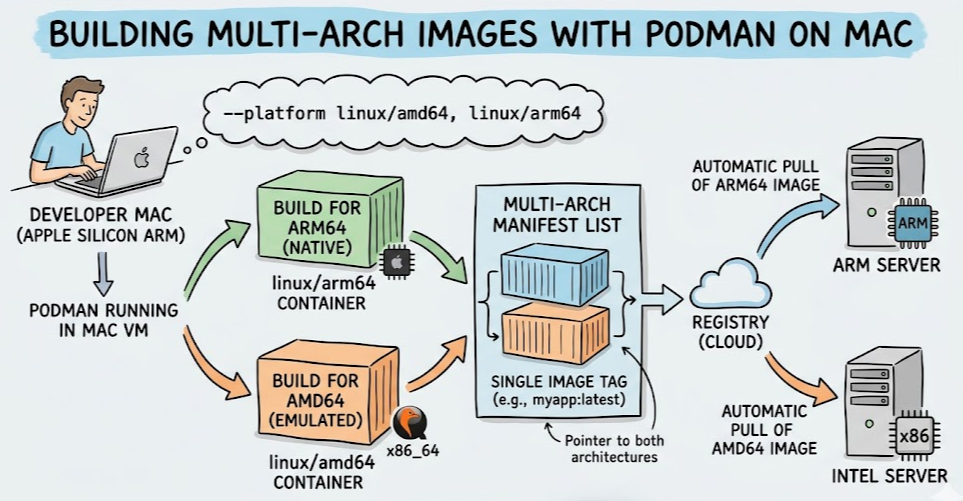
Build Multi-Architecture (Intel & ARM) Images at Once with Podman on Mac
Recently, with the fragmentation of architectures between cloud servers (Intel/AMD) and personal development PCs (Apple Silicon ARM, etc.), the need for multi-architecture container images that are not dependent on a single environment has grown. This article details how to build images that run on both Intel (linux/amd64) and ARM (linux/arm64) architectures using only Podman in…
-

Hunt with Code — Automated Signature Detector with yara-python
If a single rule is a warrior, YARA wielded by Python is a legion. The first step towards true automation beyond the command line. > What This Article Covers Why use yara-python instead of CLI, and when it becomes necessary The entire process from library installation to rule compilation, file, memory, and byte scanning Clean…
-

The Language of Malware Hunters: Creating Your Own YARA Rules
“How do I know if this file is dangerous?” To the eternal question of security analysts, YARA provides the most elegant answer. < > What this article covers What YARA is and why it’s an essential tool for security analysts The three core components of a YARA rule (meta, strings, condition) The entire process of…
-

🤖 In the Era of AI-Generated Code, Who is Responsible for Security? — The Shadow of No-Code Development
“I asked the AI to do it, and it worked well.” Did you know that a password was hardcoded into that very code? 🎯 What this article covers Security mistakes inadvertently made when developing with AI Agents Structural risks of no-code and non-developer development Why hardcoded secrets are critical (including real-world examples) Will AI’s further…
-

🍀 Did HashiCorp Betray Us? — The History of Terraform and the Real Reason OpenTofu Was Born
Open source is not free. It is, however, free. When someone tries to take that freedom away, the community responds with a fork. 🎯 What this article covers How Terraform became the standard for IaC (Infrastructure as Code) Why HashiCorp changed its license and the community’s reaction The background of OpenTofu’s birth and why it…
-

🥊 AWS Image Builder vs Packer — Which Should a Practical DevOps Engineer Use?
“I know both create AMIs, but which one should I choose in practice?” This article answers that question. < 🎯 What This Article Covers Comparison of core concepts and operating methods of AWS Image Builder and Packer Ease of use and learning curve — which one is quicker to master Selection criteria by practical scenario…
-

🏗️ The Real Reason Developers Need to Understand Infrastructure Deployment — The Misconception That “Just Write Good Code”
“My code is perfect, so why doesn’t it work on the server?” — The first deployment experience of countless developers 🎯 What This Article Covers Real problems that arise when developers don’t understand infrastructure Why DevOps and IaC (Infrastructure as Code) have become a developer’s domain How infrastructure knowledge changes code quality itself Minimum infrastructure…
-
💻 CalDigit TS4 vs TS5 vs TS5 Plus — Which Thunderbolt Dock is Right for You?
“A different dock changes your workstation. We’ll properly explain the differences between the three products.” 🎯 What This Article Covers Complete spec comparison of CalDigit TS4 / TS5 / TS5 Plus Practical performance differences from Thunderbolt 4 to 5 Key differences in port count, power delivery, Ethernet, and USB controllers “Which one should I buy?”…
-

🖊️ A Must-Have macOS Presentation Tool for IT Instructors — The Complete ZoomacIt Guide
“Why isn’t ZoomIt available on Mac?” Now it is. 🎯 What This Article Covers Why Windows’ legendary presentation tool ZoomIt came to macOS ZoomacIt’s 3 core features — Zoom, Draw, Break Timer Step-by-step guide from installation to practical lecture use A complete summary of keyboard shortcuts IT instructors/presenters must know Tips on how to effectively…